VSOC Is the New Safety Gear for You and Your Vehicles
- October 17, 2022
Digital transformation is upon us, changing how we interact with each other and the world at large. Our professional and personal lives have moved into the cloud. Everything is more connected than ever, and IoT has followed right along. In 2020, the number of IoT-connected devices surpassed IT devices for the first time.
Cars have also followed that trend: modern cars are interconnected with a wide range of wireless systems and networks. This has brought countless conveniences and efficiency gains — but it’s also introduced an entirely new range of threats and vulnerabilities. Vehicles pose a unique threat in the world of smart devices. Not only are the risks to privacy and data the same as other devices, but there are also risks to the safety of the drivers, riders, and those sharing the road. To continue to enjoy the convenience of connected vehicles, we must make them as secure as possible.
Modern vehicle technology
Cars built in the last decade are far more connected than you think. Modern vehicles contain digital components called electronic control units (ECUs), which control various vehicle features. These ECUs communicate between themselves and multiple sensors and actuators throughout the vehicle using an in-vehicle channel called the CAN bus. And it’s far more complex than you may imagine.
A modern car can have as many as 70-80 ECUs. To put that into perspective, totaling up the code powering those ECUs, a modern car has almost as many lines of code powering it as a modern jet fighter. It's a complex distributed system. The volume of interconnected systems drives the modern car experience: the navigation systems, the real-time monitoring of critical systems, the convenient connection between our phones and entertainment systems, and much more. But these systems also introduce opportunities for attackers.
For example, the CAN bus is by nature insecure. It lacks security standards we take for granted today, such as encryption and message verification. Not long ago — within the last decade — controllers within the cars lacked encryption on the microcontrollers. If an attacker got into the CAN Bus, they could essentially control any system in the vehicle because they could freely send messages and commands anywhere. Today, mission-critical controllers have encryption microprocessors. Therefore, if a controller is compromised and sends an inaccurate message, the target ECU will not act on it because it did not come from an authenticated source. That’s a huge step in the right direction, but it’s still not enough.
The biggest implication is safety. If a vehicle is compromised, it can endanger the life of the occupants and anyone around them. That’s the first and biggest consideration. But we cannot underestimate the value of private data connected to vehicles — location information, driving telemetry, etc. The more our convenience is improved, the more data these systems are able to put to use for us, the more this privacy will be at risk. Safety and privacy — these are the drivers behind modern vehicle security.
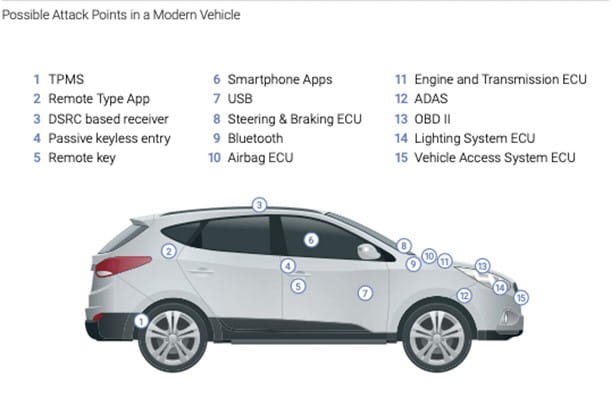
Figure 1 - Possible Attack Points in a Modern Vehicle.
Industry standards vs. OEM preferences
Establishing strict, universally adopted standards across the entire industry is exceedingly difficult because each car manufacturer architects the systems within their vehicles differently. They’re similar, but each has its own significant nuances and characteristics. Furthermore, every OEM is very protective of its system — and for a good reason. These cars and their electronic systems have evolved over years of production. Factories and entire production models are set up exclusively for them. Asking car manufacturers to completely change how they architect their vehicle networking would create substantial logistical, operational, and financial obstacles.
However, for nearly 20 years, many vehicle manufacturers have been working together to develop best practices and standards that can be applied as widely as possible. AUTOSAR (AUTomotive Open System ARchitecture) was formed in July 2003 and now has more than 280 partners (including major companies, such as BMW, Daimler AG, General Motors, Toyota, and many others). AUTOSAR aims to help vehicle and vehicle system OEMs manage the complexity of their systems more effectively and standardize the software architecture of the ECUs to improve interoperability across manufacturers.
However, due to the complicating factors described above, industry standards today are still more like suggestions or best practices than rigid standards that can be audited. Every major OEM follows them as best they can and have taken significant steps to secure their vehicles, like the encryption of the controllers and ECUs connected to the CAN bus described above.
Despite this, serious vulnerabilities remain. And given the criticality of automotive security and its implications for safety and privacy, additional solutions must be found.
This is part one of a two-part series. Read part two to learn more about the way forward in vehicle security.
To learn more about our solutions, visit our website https://us.nttdata.com/en/services/cybersecurity-servicesSubscribe to our blog

Empower Teams
As we move into 2022 and beyond, security leaders must empower their teams to have the flexibility and awareness to tackle challenges in this rapidly changing environment. CISOs can never take their eye off the technologies that dominate our field, but it’s just as essential to continue to nurture the people and processes to get the most out of those new technologies.




